A prudent man foresees evil and hides himself, But the simple pass on and are punished. -Proverbs 22:3
With Parler shutdown, Christian developers blacklisted by Visa, ministries’ bank accounts closed, and YouTube threatening to ban Christian media by only allowing “brand-safe” content, the great purge is on its way.
Now more than ever, you need to know how to combat Big Tech tyranny.
“The system of near-universal surveillance had been set up not just without our consent, but in a way that deliberately hid every aspect of its programs from our knowledge” –Edward Snowden
1. Ditch Google Chrome & Opera Browser
On a Windows machine, examine the amount of processing power Google’s Chrome browser uses up by hitting Ctrl+Shift+Esc, and you will quickly see how much tracking it is doing. Chrome sends all user activity data on any website to Google. You are even tracked in their counterfeit “incognito mode“.
Opera browser previously had a good reputation for security. Still, it has slowly eroded that position over the years to the point that it now includes built-in extensions for FaceBook Messenger, Instagram and WhatsApp that cannot be removed. These three messenger apps are very possibly the worst for user profiling, metadata harvesting, and spying.
The Dissenter browser is a modified version of the Brave browser, which incorporates the Gab social media site. Brave was produced by the software engineer behind the non-profit web browser Mozilla Firefox, and it has the added benefit of blocking all ads and tracking.
Like Brave, Dissenter is faster than Chrome and blocks ads and tracking. It also incorporates your Gab account, allowing you to comment with other Gab users on any URL. This is helpful for when comments are disabled on a website.
However, for the best online privacy, use Tor with a VPN. Tor is banned in China, so you know it’s good.
Tor can have website limitations, so this is why I recommend using Dissenter for day-to-day use and Tor for sensitive data transmission.
If you absolutely must use Google Chrome for work, limit yourself to using that one device only. Get a second, secure device for your personal browsing, email, and chatting.
2. Delete Facebook Mobile Apps & Account Data
With iOS & iPadOS 14 threatening Facebook’s surveillance program by introducing a push notification if users desire to be tracked, Facebook has gone on an all-out offensive by changing their Terms of Service to unmask any pretense of user privacy.
You must delete all Facebooks Apps (Messenger, WhatsApp, Instagram & Facebook) and your account data stored on their servers.
- How to permanently delete your Facebook account.
- How to permanently delete your Instagram account.
- How to permanently delete your WhatsApp account.
If deleting your Facebook page is not an option because of work, you must sanitize it by following our step by step guide.
There are free alternatives to WhatsApp and Facebook Messenger apps, such as the privacy-focused, open-source, tracking and ad-free apps Signal and the Tor-based Session.
3. Say Goodbye To Gmail, Microsoft Outlook, Hotmail, and Office 365
Everything you have ever read or typed in Gmail has been documented permanently by Google LLC. Chances are your Gmail email has already been compromised through a data breach at some point. Similarly, Microsoft uses AI to read the content of any emails you have hosted on Office 365, Hotmail, and Outlook.
Gmail is a social media site disguised as an email provider. Gmail automatically filters your emails and has one of the strictest blacklists of any email provider. This is incredibly scary, seeing that 1 out of 3 emails in the world is, in fact, a Gmail account. Google ultimately controls what emails you receive and can send on this platform.
ProtonMail is a Swiss end-to-end encryption email provider. Switzerland has one of the strictest privacy laws globally. This is why I would recommend connecting to Swiss or Icelandic servers when using a VPN.
4. Dump Your Android & iOS Smart Phone
Android is a mobile phone operating system that is owned and run by Google. It tracks everything you do- the contacts in your address book, the phone numbers you call, the music you listen to, the places you have visited- even when you are offline.
Your data, such as your location, is sold to private agencies so that they can even find out when you visit their stores.
Even iOS apps collect sensitive data, including clipboard information in the background.
Most smartphones do not allow users to control the hardware of their devices. Turning off WiFi, location tracking, or Bluetooth through the software of your mobile operating system does not mean it is, in reality, turned off. All this data is being used to invade your privacy.
The remedy to this is to anonymize yourself by using a de-Googled phone, which does not utilize Googles’ prying API’s or the iOS user data.
Consider purchasing Purism’s Librem 5, which has a removable battery (so you can actually turn your phone off) and a hardware kill switch that physically turns off all outbound communications, including your microphone and camera. There is also the cheaper Nokia’s 106 model to consider.
If this is not an option, use Orbot with a VPN. This uses Tor’s infrastructure to mask your mobile internet usage while securing your switched-off mobile device in a faraday cage sleeve when commuting or not using your mobile device.
A faraday cage blocks all electromagnetic communications with your device, both incoming and outgoing. However, unless you switch off your device, your changing location can still be accurately calculated using the inertial sensors in most modern smartphones.
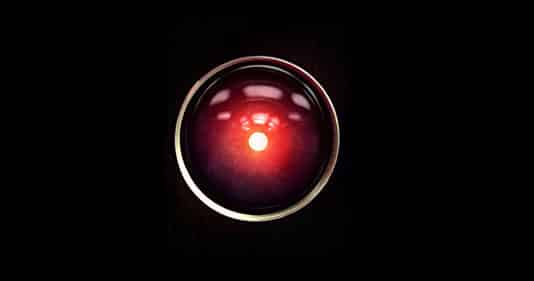
5. Remove the HAL 9000 From Your Home
2001: Space Odyssey portrays individuals stuck in a space station while being observed and governed by an evil artificial intelligence called HAL.
Today, you can have your own little AI nightmare right in your home; we call them Amazon Alexa and Google Home. Don’t forget the “OK Google”, “Hey Siri”, and “Hi Bixby” set up on your Android or iOS smart devices if you still have not dumped them.
These invasive devices are always listening for your commands while logging everything that they hear and relaying this information back to headquarters. Google has also issued patents on automating intrusive home restrictions, such as parental controls.
“Always remember Frodo, the Ring is trying to get back to its master. It wants to be found.” -Gandalf
Hidden microphones have been uncovered in Google’s appliances, such as the Nest. Before purchasing any electronic device, see what Mozilla Firefox has said about its privacy features on their *privacy not included blog.
All these devices can be very convenient. However, these devices are generating metadata such as linguistic profiling (both types) and speech-to-text, which enables a large amount of personal data to be stored in a very small amount of space. The text of a King James Bible app, for example, takes up 1,147 mega bytes (MB) in audio format. However, it only takes up 4.3 MB. in text format. This small amount of space also makes for swift computerized searches of historical content.
Automatic speech-to-text translation is also present in Google Meets, Zoom, and other voice over IP communications.
6. Throw Windows Out the Window
Windows 10 automatically updates your operating system without the ability to prevent it. This means the fundamental software of your system could completely change at any time. If Microsoft deems that you are using your computer to propagate “hate speech” or “pseudo-science,” you could very well find yourself unable to boot your pc in the future.
Secondly, Windows 10 also tracks what you do. This is called telemetry. If replacing your operating system can’t be done at this point, then following this guide to disable the default tracking functions. This will help, but it is not ideal.
Qubes OS is the most secure, Linux-based operating system for replacing Windows. Still, it requires reasonably powerful hardware, including a TPM chip (business-grade laptops and PCs typically include these), and is not the easiest to set-up and use if you are not familiar with Linux.
PureOS is easier to set up (see our review), although not as secure as Whonix, which is very complex to use as a base operating system. For this reason, it is better to run Whonix inside a virtual machine on Qubes or PureOS and use it for incognito web traversal.
7. Use A VPN
A VPN is a virtual private network. It acts as a middle man between your local internet and the wider world. By connecting to a VPN server, you limit the tracker’s ability to identify the source of your internet requests.
Mullvad VPN allows you to connect without KYC and is compatible with Tor.
NordVPN recommends using Asus manufactured routers, I tend to be suspicious of them since Asus use a system on their PC motherboards that permits them to install software on your PC without your knowledge or consent. That brings their devices onto my suspicion radar!
Ideally, you should be able to trust your VPN provider to keep your data confidential. This is because its entire business model is based on marketing its privacy services. If a data breach is uncovered, the VPN provider will lose all their business overnight.
Additionally, you can segregate your services using a VPN combined with a secure DNS service like NextDNS. You can use this to “blackhole” any known telemetry (spying) or GSOC/NSA server-destined traffic, along with getting rid of adverts at the network level.
If possible, use a router that supports VPN and encrypted DNS, so you have every device on your network protected.
8. Stop Using Google Search
Google is the number one tool the NSA and CIA use to identify people that are a threat to national security. Both these organizations have financially backed Google in their intelligence gathering initiatives.
Google search is known to manipulate search results to promote religious or political ideologies.
Google does have the best index among web browsers. This is why I would recommend using StartPage.com, which utilizes this index but prevents tracking.
Alternatively, there is Duck Duck Go that I use for research or Brave Search.
9. Intel And AMD Have Complete Access And Control Over Your PC
Intel & AMD are the leading hardware developers of central processing units (CPU). These powerful chips are the brain of every computer and are why you need so many fans to keep them cool.
Unfortunately, on post-2006 models of these chips, a hidden operating system within these chips’ firmware includes a web server. This means all computers have a backdoor of total access and control available to both Intel and AMD. Your system can be powered on or shut down at will, all the files on your system examined, keyboard inputs, and display outputs captured.
These are known as the Intel Management Engine (ME) and AMD Platform Security Processor (PSP).
Apart from using pre-2006 CPU chips or installing Coreboot or Libreboot firmware (which is very dangerous and could destroy your computer) that are only compatible with limited CPU models, there is little you can do to counter this. This is why it is vitally important that you implement as many of the above resolutions as possible. Otherwise this may prove to be a solution.
Purism is developing a ME disabled laptop, which you should keep an eye on, and System76 offers Coreboot laptops.
10. Stay On Top Of Tech Developments
There is new illiteracy you must overcome. It is not the inability to read, but rather the inability to use technology appropriately. You must understand how tech works to protect yourself and the ones you love from being exploited.
We can only imagine the damage a ruthless dictator like Hitler could have achieved if he had the data streams available to him that are present today through Big Tech. In fact China has utilised surveillance technology in the enforcement of their social credit system.
Expect BIG changes in how you interact with the internet. People are waking up at last, and we praise God that Christians want to take action to protect their identity and privacy online.
Solid is an up-and-coming project from Tim Berners-Lee, pretty much the man that invented the internet. Tim has expressed grave concerns with the lack of individual freedom on the internet and has set out to “reinvent” it on the Solid platform. This is certainly on my “one to watch” list for the near future.
Likewise, the Beaker browser is a reasonably secure browser that permits peer-to-peer self-hosted websites with the ability to share these with others on the browser. This may become a necessity as more and more internet hosting is purged of Christian content under the guise of hate speech.
If you have a website (like TheoNerds.net) with Christian content, you may find yourself censored out of existence. Still, the content may be valuable enough to want to continue sharing – Beaker browser permits this with ease, bypassing any hosting servers beyond your PC (as long as it is kept switched on!).
We at TheoNerds strive to keep Christians up-to-date on tech news from an unashamedly Biblical worldview. Consider joining our email list to stay updated.
Excellent! Thank you so much for the great research and suggesting so many alternative options. I was aware of several of them, but I also learned about a few new ones from your article. Very helpful. Glad I discovered this… Read more »
Great stuff! Now I just need to convince all my people to get off of WhatsApp and Zoom and instead swap over to Signal 😛 This article was much needed for me; I’ve been attending a Scripture memorization group for… Read more »
Good stuff, glad you got some use from the article.
Your feedback is appreciated.